Over the last decade, business email compromise attacks have become the most common and expensive form of cybercrime, costing businesses over $50 billion according to FBI data. These sophisticated scams target businesses of all sizes, from small, local companies to major corporations, by infiltrating email communications and impersonating trusted contacts.
Cybercriminals conducting business email compromise attacks often pose as executives, vendors, or business partners to manipulate employees into transferring funds or sharing sensitive data. The rise of artificial intelligence (AI) tools has made these impersonation attempts more convincing as scammers use it to appear more realistic.
This article examines how business email compromise works, common features, and how criminals use it to facilitate authorized push payment fraud to trick victims into transferring funds. It also outlines the latest techniques and provides practical steps to protect your organization.
What Is Business Email Compromise and Why Is It a Threat?
Business email compromise happens when cybercriminals target organizations through sophisticated email schemes to steal money or data. Unlike typical phishing attacks that cast a wide net, business email compromise scammers research their targets and personalize their emails to trick specific employees who can access company finances or sensitive information.
On average, small businesses face $80,000 in losses per incident, while larger corporations have lost millions in single attacks. These numbers continue to rise as criminals use more advanced techniques.
Often, businesses only discover the attack after money has been transferred through multiple overseas accounts, making it nearly impossible to get the funds back. This combination of sophisticated tactics and severe financial impact makes business email compromise a critical risk that requires specific prevention strategies and employee training.
How Do Business Email Compromise Attacks Work?
Business email compromise attacks begin with extensive research as criminals work to identify key employees and study their communication patterns. They often focus on staff with financial authority, examining their social media profiles, professional networks, and public communications to build detailed profiles.
Then, they launch attacks through multiple methods:
- Phishing Campaigns: Attackers send emails that appear to come from trusted sources, asking employees to enter their login credentials on fake websites. These stolen credentials give attackers access to legitimate email accounts.
- Email Spoofing: Criminals create addresses that look nearly identical to real ones. An attacker might change a single letter or add a hyphen to "accounting@company.com," making it "accountlng@company.com" or "accounting-team@company.com." These small differences often go unnoticed.
- Malware Deployment: Attackers plant malware through infected email attachments or links. This malware can monitor email traffic, steal passwords, or give criminals direct access to business networks. With this access, attackers can read emails, study internal processes, and plan more targeted fraud attempts.
Social engineering also makes business email compromise attacks more successful. Criminals exploit human psychology by creating artificial urgency, impersonating high-ranking authority figures, or taking advantage of inattention to routine business processes. An attacker might impersonate a CEO requesting an urgent wire transfer or a vendor sending an invoice with "updated" payment details.
The goal of these social engineering tactics is to trigger an authorized push payment, where the employee believes they're making a legitimate transfer when they’re actually sending funds to criminals.
How Do Criminals Use AI In Business Email Compromise?
Artificial intelligence has transformed business email compromise attacks from simple email spoofing into sophisticated impersonation schemes. Criminals now use AI language models to analyze and mimic an executive's writing style, with emails that match their tone, vocabulary, and even common grammatical patterns.
Deepfake technology adds another layer of deception, allowing criminals to create audio and video that copies executives' voices and appearances. For instance, employees might receive a fraudulent email followed by a video call that appears to show their CEO requesting an urgent wire transfer. Email, followed by audio or video, makes the scam appear more legitimate.
Machine learning also helps criminals improve their attacks by analyzing patterns in corporate communications. These tools can help them determine the best time to send fraudulent emails, figure out which employees to target, and write emails that bypass security. Technology also allows criminals to launch multiple customized attacks simultaneously, increasing their chances of success.
Which Employees Do Business Email Compromise Attackers Target Most?
Financial teams face the highest risk in BEC attacks because they control payment systems and handle wire transfers. Common targeted roles include:
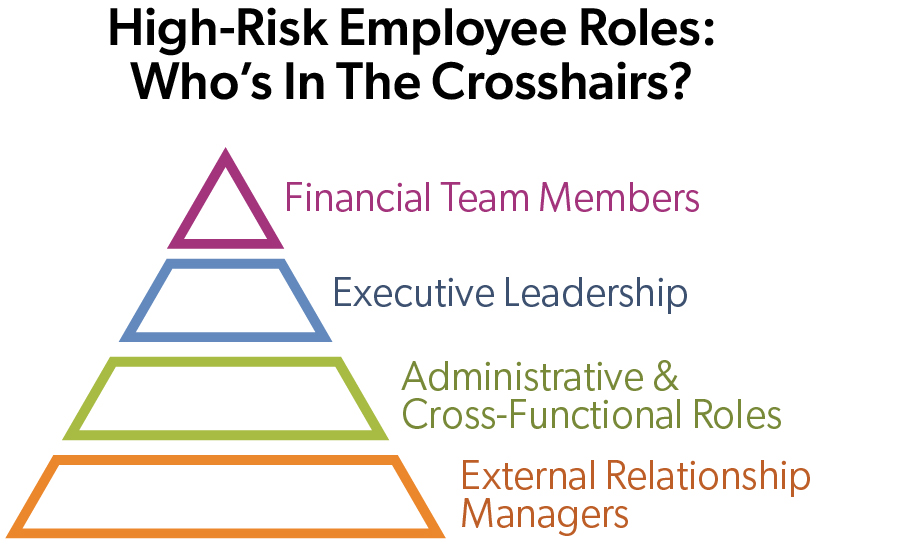 Accounts Payable Staff. These employees make prime targets because they handle payment systems and manage wire transfers. Their direct involvement in payment approval processes makes them especially valuable to criminals.
Accounts Payable Staff. These employees make prime targets because they handle payment systems and manage wire transfers. Their direct involvement in payment approval processes makes them especially valuable to criminals. - Controllers and Accounting Managers. Criminals target these roles because they can approve large transactions and often oversee multiple financial processes, making their compromised accounts particularly valuable.
- C-Suite Executives. Their email accounts attract attackers because they can be used for impersonation schemes. Public speaking engagements and media presence provide criminals with details to craft convincing fraudulent messages.
- CFOs and Treasury Executives. These positions face increased targeting because they have direct access to company bank accounts and can authorize significant financial transactions without additional approvals.
- Human Resources Personnel. HR teams become targets during hiring periods and benefits enrollment. Criminals request W-2 forms, salary information, and employee banking details while posing as executives or new hires, aiming to steal personal data for identity theft or future scams.
Criminals also exploit vendor relationships with business email compromise through invoice manipulation and payment redirection schemes. They target both sides of these relationships — compromising supplier email accounts to send fake invoices or impersonating vendors to change payment details.
What Is Authorized Push Payment Fraud And How Does It Relate to Business Email Compromise?
Authorized push payment fraud occurs when criminals deceive employees into willingly authorizing payments to fraudulent accounts. In these schemes, the payment appears legitimate because an authorized employee initiates the transfer, which makes it harder for banks to flag the transfer as suspicious activity.
In sophisticated financial scams, business email compromise and authorized push payment fraud often merge. A typical attack combines compromised email accounts with social engineering to request wire transfers that seem authentic. The scammer might use a spoofed executive email account to direct an employee to pay a "new" vendor account, or they might infiltrate vendor communications to change payment details for legitimate invoices.
How To Detect and Respond to Business Email Compromise Attempts
Every employee in your organization should know these warning signs of potential business email compromise:
- Irregular Payment Patterns: Watch for requests that bypass standard procedures, such as authorized push payments to pay new bank accounts or changes to established vendor payment details without proper documentation.
- Time-Pressure Tactics: Be alert to messages creating artificial urgency through phrases like "immediate action required" or threats about missed deadlines and financial penalties. Criminals count on rushed decisions leading to mistakes.
- Unusual Communication Methods: Question emails from executives asking to communicate through personal addresses or messages from vendors requesting sensitive data through unfamiliar channels.
- Grammar and Design Discrepancies: Notice subtle differences in email addresses, contact information, or writing style that might indicate impersonation attempts.
How Should Companies Respond to a Business Email Compromise Attack?
The first 24 hours after discovering a business email compromise attack are critical for minimizing damage. Immediately contact your business’s financial institution to report fraudulent transfers and request an emergency recall of funds. Sometimes banks can freeze transactions if they are notified quickly, and the payment is a form that can be recalled or stopped.
When you suspect fraud, take these immediate steps:
- Stop all related financial transactions
- Alert IT security to examine affected systems
- Save all evidence and document the timeline
Report the incident to your local FBI field office, the Internet Crime Complaint Center (IC3), local police, state consumer protection offices, and your cyber insurance carrier, if applicable.
Follow up with a thorough security review examining how the attack succeeded and where defenses failed. This should include investigating compromised accounts, strengthening access controls, updating security protocols, enhancing employee training, and evaluating vendor security practices. Consider bringing in cybersecurity experts for an independent assessment to prevent future attacks.
The First 24 Hours After a Business Email Compromise
Hour 1: Immediate Containment
Key Actions:
- Contact your financial institution to freeze accounts and stop pending transfers
- Isolate affected systems and disable compromised email accounts
- Alert your IT security team or managed service provider
- Document the exact time the attack was discovered
Hours 2-4: Evidence Collection
Key Actions:
- Preserve all original fraudulent emails (do not delete)
- Screenshot all relevant communications
- Document transaction details, timestamps, and involved parties
- Begin creating a chronological attack timeline
- Secure any remaining digital evidence
Hours 5-8: Notification & Reporting
Key Actions:
- Report to FBI Internet Crime Complaint Center (IC3)
- Contact local FBI field office for substantial losses
- File police report with local authorities
- Notify cyber insurance provider if applicable
- Alert your legal counsel
Hours 9-16: Damage Assessment
Key Actions:
- Conduct preliminary investigation to identify attack vector
- Determine scope of compromise (which accounts, systems affected)
- Assess financial impact (amounts transferred, potential losses)
- Evaluate data exposure risk
- Begin password resets for all potentially affected accounts
Hours 17-24: Recovery Initiation
Key Actions:
- Deploy enhanced monitoring on all financial systems
- Initiate secure account recovery procedures
- Begin implementing immediate security improvements
- Prepare communication for affected stakeholders
- Assemble response team for ongoing recovery efforts
What Are Best Practices To Prevent Business Email Compromise?
Preventing business email compromise attacks requires a multi-layered approach. Strong verification protocols for all authorized push payments are the first line of defense against business email compromise. Financial teams must confirm all payment changes through multiple channels. When a vendor emails new bank account details, verify through a phone call to their established contact using a number from existing records, not from their email.
Email security depends on advanced filters to detect spoofed addresses, multi-factor authentication on all accounts, and domain monitoring services to catch impersonation attempts before they start.
System security requires prompt software updates, current antivirus protection, regular data backups, and quarterly security protocol reviews.
Financial controls should establish clear authorization limits, implement mandatory dual approval for transactions above set thresholds, and create separate processes for routine versus emergency payments to prevent exploitation of rushed approvals.
How Can Employee Training Help Prevent Business Email Compromise?
Regular training helps your employees recognize, prevent, and report business email compromise attempts. The most successful training creates awareness, raises confidence, and promotes suspicion, so employees feel empowered to verify suspicious payment requests.
Focus employee training on real-world attack patterns, like:
 Messages with urgency tactics or unexpected requests
Messages with urgency tactics or unexpected requests - Suspicious sender addresses with subtle variations
- Requests that bypass standard payment procedures
- Unusual formatting, grammar, or communication channels
Examining the full attack sequence to fully understand the relationship between business email compromise and authorized push payment fraud
Reinforce employee training with strong and clear internal policies for:
- Verifying payment changes and wire transfer requests
- Reporting suspicious communications
- Handling sensitive information securely
- Managing vendor relationships and payment changes
Maintain ongoing awareness through monthly security updates, team discussions of recent attempts, and regular simulated phishing tests to identify weaknesses and measure program effectiveness.
Protecting Your Organization from Business Email Compromise
Business email compromise threatens organizations of all sizes, combining sophisticated technology with social engineering to bypass traditional security measures. The rise of artificial intelligence and authorized push payment fraud has made these attacks more convincing and harder to detect. However, organizations can defend themselves through a combination of strong payment controls, employee training, and security awareness.
Successfully preventing these attacks requires commitment and training of every employee. From C-suite executives to accounts payable staff, each employee plays a vital role in maintaining security. By implementing these strategies, your business can reduce the risk of falling victim to business email compromise.





