Account takeover fraud, when a hacker gets into one of your online accounts, is a significant threat to people, organizations, and businesses. In fact, recent data shows that about one-third of people, or more than 80 million U.S. adults, have experienced account takeover fraud, and attacks continue to increase as criminals use automation and artificial intelligence in their efforts. The personal behaviors that can lead to account takeover directly impact businesses, as both employees and customers can unknowingly bring risks into the corporate environment.
Understanding how account takeover fraud happens and implementing effective account takeover prevention strategies is the first step to protect your company's reputation, sensitive information, and financial assets.
What Is Account Takeover Fraud?
Account takeover fraud occurs when criminals gain unauthorized access to a user's account, often through stolen login credentials or social engineering tactics. When they gain control of an account, they can cause extensive damage to your business's finances and reputation.
When hackers access online banking accounts, the stakes are high. Account takeover fraud can lead to:
-
- Fraudulent payments & transfers
- Reputational damage
- Operational disruptions
- Identity theft
Business Email Compromise (BEC) is a type of account takeover fraud involving criminals accessing work email accounts. This extremely common account takeover fraud allows hackers to:
-
- Use legitimate email accounts to impersonate executives or finance department employees
- Initiate fake financial transactions
- Redirect legitimate payments to criminal-controlled accounts
- Access sensitive company information
Financial account takeover fraud is different from other types of fraud because of the potential for criminals to cause significant damage over the long term. Unlike isolated incidents, such as a single instance of wire transfer fraud, financial account takeover fraud sometimes continues over a long period of time if it goes undetected. This extended access can lead to sizable financial losses and prolonged identity theft issues.
While financial accounts remain primary targets, cybercriminals also exploit vulnerabilities in corporate cloud storage, employee credentials for government services, company social media profiles, and even business-related subscription services. Social media account takeovers are particularly concerning for businesses and organizations, as they can severely damage brand reputation, erode customer trust, and lead to significant financial and operational consequences.
How Does Account Takeover Fraud Happen?
An important part of account takeover fraud prevention is learning how criminals most often access online accounts, whether business or personal. By understanding their methods, you can work with your IT department to strengthen your prevention strategies and reduce the risk of account takeover fraud at your business.
AI-Powered Social Engineering: Criminals use generative artificial intelligence to create highly convincing phishing attacks that are difficult to detect. AI allows them to:
-
- Generate grammatically perfect, personalized phishing emails that mimic your vendors, bank, or executives
- Create voice clones of executives or colleagues to authorize fraudulent wire transfers or request sensitive information
- Produce deepfake videos to bypass identity verification in video calls or banking applications
Because AI makes it possible to impersonate trusted individuals with unprecedented accuracy, always verify all unusual requests through a secondary communication channel, even if the voice or video appears authentic.
Phishing and Social Engineering: One recent study shows that 74% of account takeover attacks begin with phishing. Criminals use misleading emails, phone calls, texts, or social media to trick people into giving them their login credentials or sensitive information. The hackers often pretend to be trusted people, like bank employees, executives, or vendors. A particularly concerning trend involves scammers impersonating banks through phone calls that appear to come from legitimate financial institutions, including First Business Bank. This tactic is happening across the country, affecting clients of banks nationwide. Criminals use technology to make their phone numbers appear as though they’re from the bank, creating a false sense of legitimacy. During these calls, they may request sensitive information such as account numbers, Social Security numbers, passwords, PINs, or one-time passwords (OTPs).
Legitimate banks will never call and ask you to provide sensitive information. If you receive such a call, even if the caller ID appears to be from your bank, disconnect immediately and call your bank directly using a number you know is legitimate, such as the one on your bank statement. Report the incident to your Treasury Management officer immediately so they can alert other clients and help protect against future attempts.
Scammers often create a false sense of urgency to pressure you into acting quickly without thinking. Take your time to verify any unexpected requests, and remember: when in doubt, hang up and call back using a verified number.
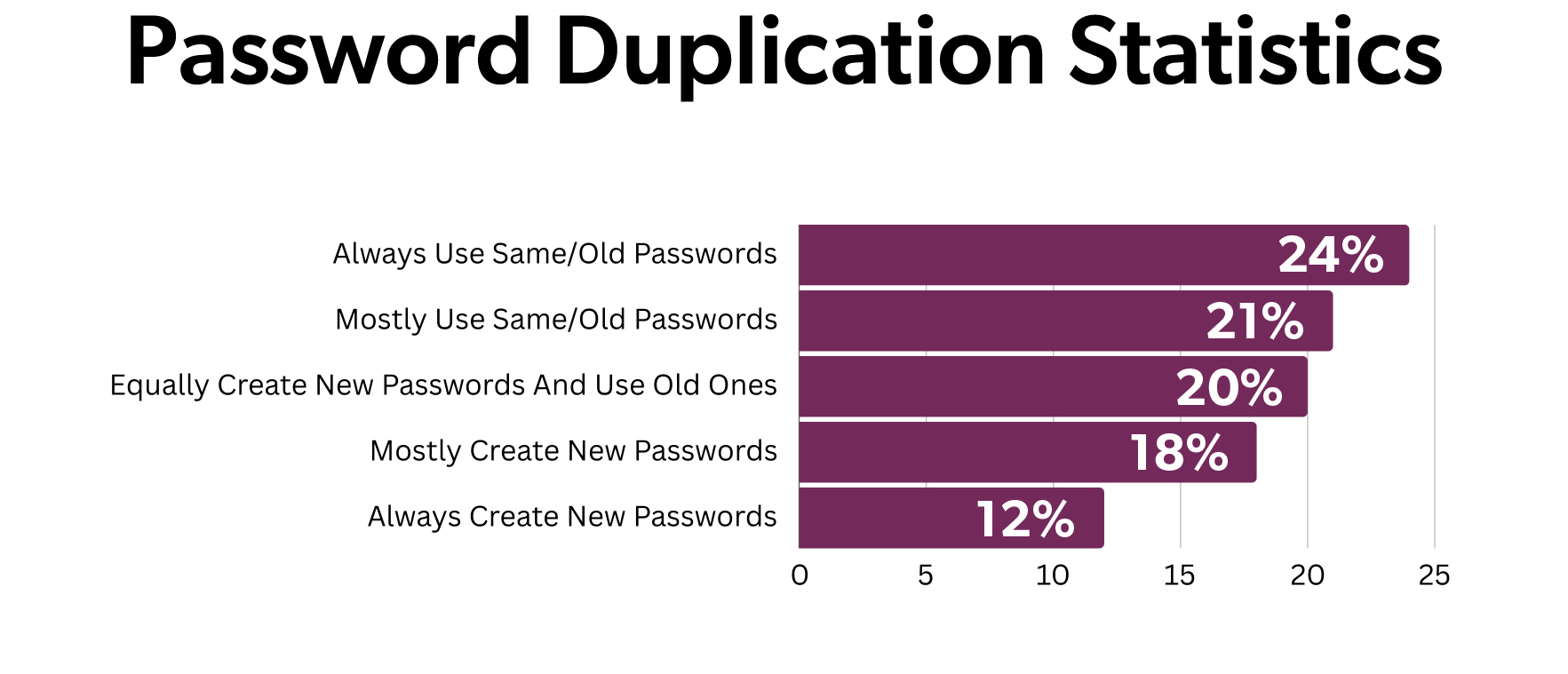
Credential Stuffing: Every time you make a new account online, you typically have a login username and a password. And every time there’s a data breach involving stolen usernames and passwords, criminals often try to use them to log in to other accounts, sometimes leveraging automated tools to test large numbers of credentials quickly. Unfortunately, many people reuse passwords across multiple accounts, which leaves them vulnerable to account takeover fraud. In fact, only about 12% of adults report making a new, unique password for each account.
Session Hijacking (AiTM Attacks): Criminals use sophisticated "Adversary-in-the-Middle" (AiTM) techniques to steal session cookies, which are digital tokens that prove you've already logged in. By hijacking an active session, they can bypass multi-factor authentication because they're essentially "riding along" on your authenticated session. That’s why logging out of accounts when finished and clearing browser cookies regularly are important security practices.
SIM Swapping: Criminals contact mobile carriers and impersonate account holders to transfer phone numbers to devices they control. Once they control a phone number, they can intercept text messages containing authentication codes, password reset links, and banking alerts. This is why SMS-based multi-factor authentication is no longer considered the most secure option.
Malware and Infostealers: Harmful software programs can be installed on your devices when you click on links in phishing emails, download suspicious attachments, visit compromised websites, or connect to unsecured public Wi-Fi. Modern infostealers are dangerous because they automatically harvest passwords saved in browsers, authentication cookies, and credentials stored in applications without requiring you to do anything. These programs operate silently in the background, gathering login information and sensitive data that criminals sell or use for account takeover attacks.
Security Gaps: Weak organizational cybersecurity practices often make accounts vulnerable. These may include weak password policies, lack of multi-factor authentication, outdated software, or insufficient employee training on cybersecurity best practices.
What Are Common Signs of Account Takeover Fraud?
Signs that hackers accessed an account will vary by the type of account, but these are some of the most common symptoms of potential account takeover attempts. Pay close attention to anything out of the ordinary.
- Unusual account activity. Watch for unusual account activity like several failed login attempt alerts, transactions that deviate from normal patterns, or logins from unfamiliar locations.
- Alerts from your bank. Financial institutions play a crucial role in detection. They may send alerts about large or out-of-pattern transactions, login attempts from new locations, or changes to account details. Take these notifications seriously and respond promptly.
- Client feedback. Customer complaints can also signal potential fraud. Make sure to investigate further if your customers report unauthorized transactions, difficulty accessing their accounts with you, or unexpected changes to their account information.
How Do Businesses Prevent Account Takeover?
Your business has a duty to implement strong account takeover prevention strategies to reduce the risk of account takeover fraud. Ignoring these can result in major financial losses, damage to your organization’s reputation, and possible legal liability. Prevent account takeover by implementing the following strategies:
- Strong Password Policies: Require employees to use complex, unique passwords for each account. Modern cybersecurity guidelines recommend prioritizing password strength and uniqueness over frequent password changes. Forced periodic password changes often lead employees to create predictable, weaker passwords (such as changing Summer2024! to Autumn2024!). Instead, require password changes only when there's evidence of a compromise or breach. Prohibit reusing passwords across accounts and strongly encourage the use of password managers to securely generate and store unique passwords for every account.
- Use Multi-Factor Authentication (MFA): Implement MFA for all accounts, especially those with sensitive information, like online banking. Multi-factor authentication requires a second verification after logging in. However, SMS and voice-based codes are vulnerable to SIM-swapping attacks, where criminals hijack your phone number to intercept codes. For stronger security, we encourage Business Online Banking clients to use soft tokens, which is an app on your phone, or step-up authentication, which involves a text or a phone call with a code.
- Educate Employees Regularly: Implement a continuous training program to teach your staff to recognize phishing attempts and social engineering tactics. Running simulated phishing campaigns can help reinforce this training.
- Update Software Promptly: Work with your IT department or vendor to regularly update all software, including operating systems, applications, and security software. Apply security patches right away when they're released to reduce risks.
- Monitor Accounts: Reconcile bank accounts daily to promptly catch any unauthorized payments. Work with your bank to implement fraud prevention tools and alerts for unusual account activities.
- Implement Session Security Practices: Work with your IT department to configure automatic session timeouts for inactive accounts, require re-authentication for sensitive transactions, and implement policies that detect and alert on suspicious session activity such as logins from different locations in a short time period. Encourage employees to log out of accounts when they’re finished rather than just closing a browser window.
- Limit Access To Accounts: Only allow employees access to accounts and sensitive information that they need to perform their jobs. Regularly review who can access accounts, especially when employees change roles or leave. Train new employees rigorously on security protocols.
- Upgrade Network Security: Work with your IT department or vendor to implement firewalls and encryption to protect data. Conduct regular security audits and penetration testing. Use network segmentation and VPNs for remote access.
- Review Incident Response Plans: Develop plans to respond to account takeover fraud. Document steps to take, who to contact, and regularly update and test the plan, ensuring all staff members understand their responsibilities.
Steps to Take When Account Takeover Fraud Occurs
Despite your best efforts to prevent it, account takeover fraud can still happen, and knowing what to do is the first step to fixing it. Criminals often go to great lengths to hide their fraud, including redirecting alerts and notifications to minimize account takeover fraud detection, which means businesses need to be on guard and prepared to act quickly when they suspect fraud. Here are some steps to take:
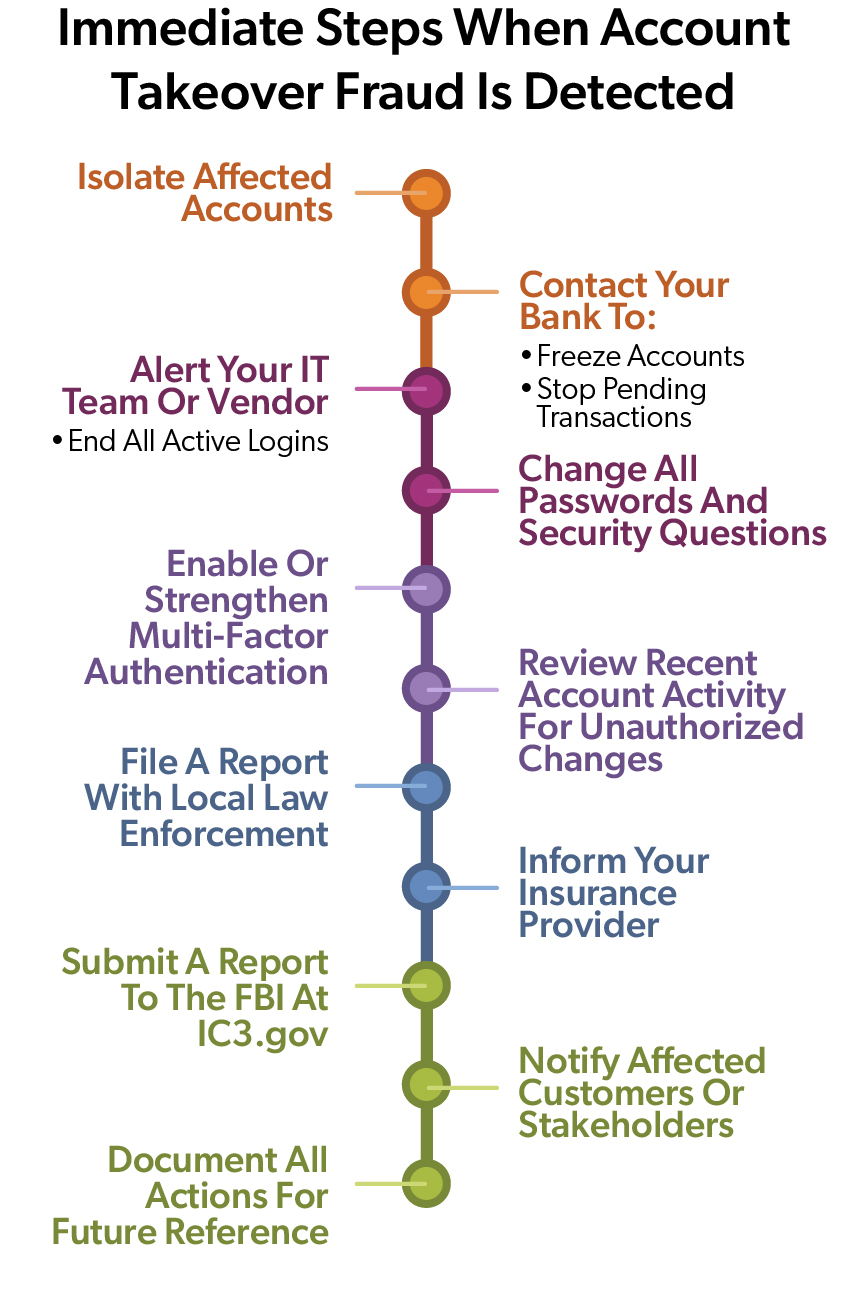
- Act Immediately: Isolate the accounts that are affected and work with your bank to freeze accounts and stop pending transactions. Alert your IT team or vendor, change passwords, enable MFA, file a report with law enforcement, inform your insurance provider, and submit a report to the FBI at IC3.gov.
-
- Check for AI-generated communications: Review recent emails, voice messages, or video calls that may have been AI-generated by attackers using compromised accounts to impersonate executives or employees.
- Check for AI-generated communications: Review recent emails, voice messages, or video calls that may have been AI-generated by attackers using compromised accounts to impersonate executives or employees.
-
- Revoke Active Sessions: In addition to changing passwords, force all active sessions to end across all affected accounts and devices. This ensures that stolen session cookies become invalid. Work with your IT team to clear browser cookies and cached credentials on potentially compromised devices. For critical accounts like email and banking, enable "sign out of all devices" or "end all sessions" features if available.
- Investigate the Breach: Have your IT team or a cybersecurity expert examine the breach in detail. Identify how the attackers gained access, what information was compromised, and determine the timeline of the attack. Collect and preserve evidence for potential legal action. Cybersecurity insurance may cover the cost of this investigation.
-
- Determine whether the attack involved AI-powered phishing, SIM swapping, session hijacking, or infostealer malware, as each requires different remediation approaches
- Check for signs of persistent access through stolen cookies or sessions that may allow re-entry even after password changes
-
- Strengthen Security Post-Breach: Review and update security policies based on lessons learned from the investigation. Implement additional security measures and train employees, including training for the vulnerabilities exploited in the attack.
Strengthening your account takeover fraud prevention strategy is an ongoing process that must evolve with the shifting tactics of cybercriminals. By staying informed about emerging threats, regularly updating your security measures in collaboration with your bank, and fostering a culture of security awareness within your organization, you'll be better equipped to minimize the risk of account takeover fraud and mitigate potential damages.
Updated: 3/27/2026





